Transmission exclusively using VPN
Written by pmd - - no commentsI would like to have my transmission client to exchange data only through a VPN.
Firewall
First of all, it is necessary to set some rules so the 'debian-transmission' user (running transmission) can only route through the VPN:
# after these 3 first rules, transmission cannot access internet
$ sudo iptables -A OUTPUT -m owner --uid-owner 'debian-transmission' -o tun0 -j ACCEPT
$ sudo iptables -A OUTPUT -m owner --uid-owner 'debian-transmission' -o lo -j ACCEPT
$ sudo iptables -A OUTPUT -m owner --uid-owner 'debian-transmission' -j REJECT
# marking all packets used by users different than 'debian-transmission' with '42'
$ sudo iptables -t mangle -A OUTPUT -m owner ! --uid-owner 'debian-transmission' -j MARK --set-mark 42
$ sudo iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE
$ sudo sysctl -w 'net.ipv4.conf.eth0.rp_filter=2' # reverse path filtering
FYI: These rules will be set only until next reboot.
FYI: To get a complete presentation of all the netfilter rules, you can use these commands :
$ sudo iptables -vL -t nat
$ sudo iptables -vL -t mangle
$ sudo iptables -vL -t raw
$ sudo iptables -vL -t security
FYI: To display rules so you can verify there are good :
If you are sure that these iptables rules we set are OK, you can make them permanent (resistant to reboot):
$ sudo dpkg-reconfigure iptables-persistent # if already installed
Tap yes to both prompts. Verify it was correcly taken into account especially interfaces :
Done, these rules are persistent: transmission cannot communicate without an active tun0 interface (VPN).
Routes
The strategy I used is this one:
- all packets not marked '42' following main route table
- all packets marked '42' following route table named '42'
Create a systemd .service to create and populate route table '42' when Pi3 starts:
We will wait to find an IP address containing "192", then we will create the new table "42" and copy all rules from main table to "42" table.
[Unit]
Description=Copy the route of main table to table 42 at system startup
After = network-online.target
Wants = network-online.target
[Service]
Type=oneshot
#ExecStart=/bin/bash -c "while ! [[ -n $(ifconfig | grep 192) ]]; do sleep 1; done; ip rule add fwmark 42 table 42; ip route show table main | while read LINE; do ip route add $LINE table 42; done"
ExecStart=/bin/bash -c "while ! [[ -n $(ifconfig | grep 192) ]]; do sleep 1; done; ip rule add fwmark 42 table 42; ip route show table main | grep -v tun0 | while read LINE; do ip route add $LINE table 42; done"
[Install]
WantedBy=multi-user.target
We reload systemd to update with the new service we made and make the service execute at system startup.
$ systemctl daemon-reload # Run if *.service file has changed
# Try the new service
$ sudo systemctl start copy_route_pmd.service
# If OK (check tables main and 42), set service to execute at startup
$ sudo systemctl enable copy_route_pmd.service
Now, debian-transmission will use main table to route packets, and users different than debian-transmission will use the table 42.
Link to article to check routes
openvpn
Make sure that you let openvpn push new rules in main route table in order to use the VPN.
Now that openvpn made up tun0 interface, check that the routes are respected:
$ sudo -u debian-transmission wget -qO- ifconfig.co
These two commands will return different IP address!
transmission
Verify that transmission-daemon is run by correct user:
Check your visible torrent IP with this: https://torguard.net/checkmytorrentipaddress.php
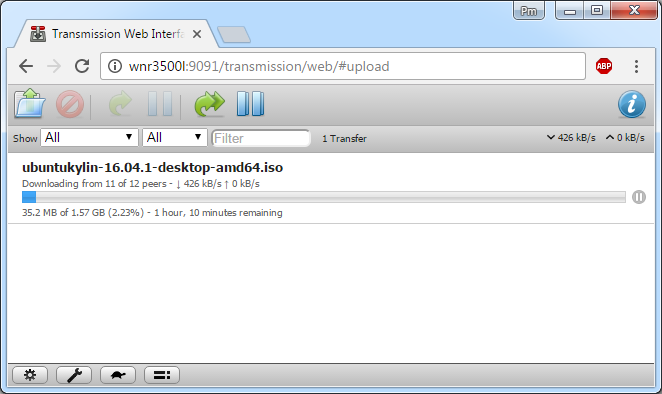
Access to transmission web interface will require nginx
nginx
Install nginx:
Edit the default configuration:
If the machine does not have an IPv6 address set, you need to comment this line :
Replace section location by this :
proxy_pass http://127.0.0.1:9091;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
}
Restart nginx:
Access your interface worldwide using: http://yourIPadress/transmission/web/
DNS leak
To prevent DNS leak and/or not to rely on the router you are connected to the internet, modify the file:
nameserver 208.67.222.222
nameserver 208.67.220.220
#Google Servers
nameserver 8.8.8.8
In fact I want to set the DNS servers directly in the Raspberry Pi, because it allows me to remove the default route to the router in table 42 and keep it as tidy as possible.
Then reboot the Pi 3:
You can now check that these are the first DNS server is use:
# Generated by resolvconf
#OpenDns Servers
nameserver 208.67.222.222
nameserver 208.67.220.220
#Google Servers
nameserver 8.8.8.8
domain home
nameserver 192.168.1.1
From your Pi3, check the DNS leakage from this website: https://dnsleaktest.com/